HALOWEB IS OPERATIONAL DURING THE LOCKDOWN AND WE’LL DO OUR BEST TO DELIVER YOUR ORDER AS QUICKLY AS POSSIBLE.
We’ll deliver your order via courier and you can still get help via our WhatsApp, email and phone.
Haloweb Fast Secure Web Hosting, Domain Registration, and Internet Services
Fanatical Service, Cost Effective Web Hosting Products, And Zero Risk
H aloweb provides web hosting services to individuals and businesses, our website hosting plans are very flexible and you are even able to request custom plans according to your specific requirements, Haloweb also offers website design options starting at as little as R500 for a single page portfolio site.
Domain availability checker
Pricing
Web Hosting Plans & Pricing
Our Fibre Providers
A list of our Fibre Broadband Providers offering a much higher chance of availability in your area.

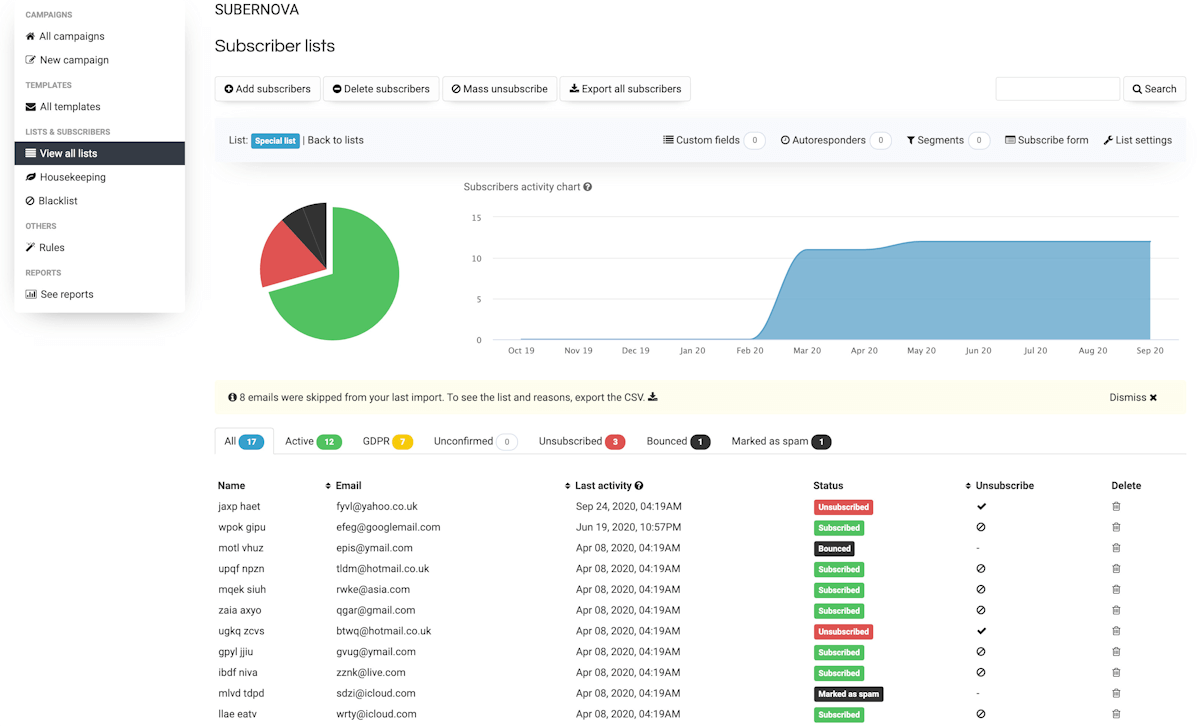
SECURE SERVER Management
Safe and Secure Web Hosting & Backups
Lightning Fast Servers
Haloweb Has put a lot of resources into ensuring that our clients websites are running at the fastest speed possible and that they are as secure as we can make them, website speed is important to Google and could be one of the deciding factors in your search engine rankings.
cPanel - Control Panel
All of our web hosting plans come with a full featured cPanel control panel where you can setup as many email accounts as you need or even install a web app.
Top Notch Support
When it comes to support Haloweb is the best in the industry with our 24 /7 clients support desk where we often go the extra mile and depending on the problem we often provide remote support to assist our clients.

One Click Installer
Looking to setup your own WordPress or Joomla website, with over 100 web applications our online installer will do it for you in a matter of a few clicks.
Get your business online today
Web Hosting
- 99.9% Uptime Guarantee
- Reliable & Secure
- Powered by cPanel
Starting From
R19.00
per mo
Reseller Hosting
- 99.9% Uptime Guarantee
- WHM for Management
- One Click Installer Included
Starting From
R399.00
per mo
SSL Certificate
- Up to 256-bit Encryption
- Free Reissues Included
- Browser Compatibility
Starting From
R216.77
per yr
Site Builders
- Quick & Easy to Use
- Choose from 100’s of designs
- Build Professional Websites
Starting From
R443.77
per mo