Android ransomware family named Charger discovered on Google, causing Google to remove an app from their Play Store.
Posing as battery saving software, Energy Rescue collects data from your SMS’s and contact list. It uploads the information to the criminal’s servers, eventually locking your machine.
This ransomware comes with a note threatening users with publishing their information should they refuse to pay.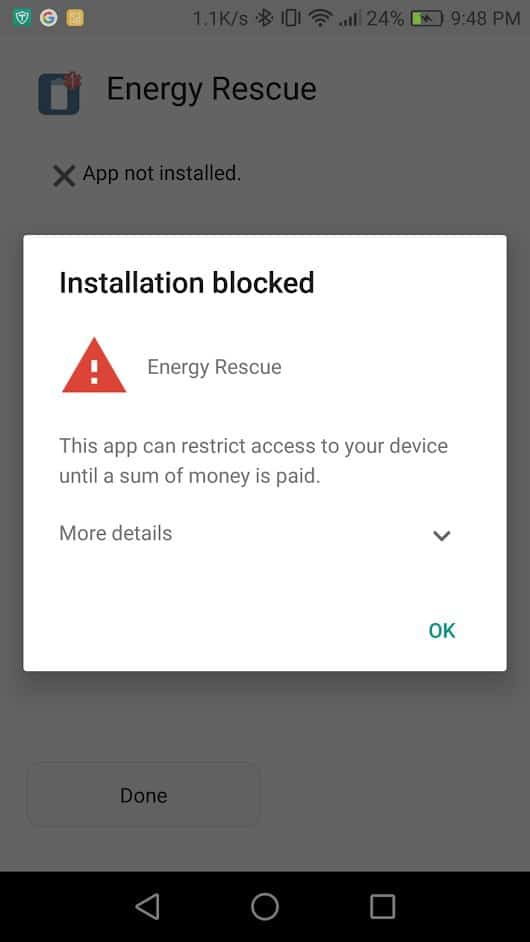
Some of the threats are empty researchers did not observe the app ex-filtrating a number of the data the crook uses and threatens to reveal. For instance bank card particulars and account information.
Lately, this kind of ransomware has been referred to as “Doxware”.
The app was discovered by Security Firm Check Point when a client installed the app on their machine and the machine was quarantined.
Researchers discovered a number of issues that stood out after analyzing the ransomware compared to earlier Android ransomware families.
Ransomware contaminated devices being the biggest of these. Earlier threats relied on droppers to gain a foothold on contaminated devices.
These can be small apps with restricted malicious conduct, bypassing Google’s Play Store Security checks. Later asking for customers administrator rights.
These apps would download the actual ransomware at later points if they are able to convince users to grant them admin rights.
Charger is quite sophisticated
Check Point says that the EnergyRescue app contained all of the malicious code right from the start.
Making “Charger” quite a sophisticated ransomware and completely different.
Regardless of placing all its code in a single basket, researchers say that the Charger authors have performed a very good job at disguising the ransomware’s malicious conduct.
To begin with, all strings were encoded as binary arrays, making it extremely difficult to inspect the app. Even by veteran security researchers.
Second, they loaded malicious code from encrypted sources, so that Google’s detection engine couldn’t reach to examine.
Third, they flooded the phone with useless commands, so that they can conceal malicious operations from a human’s manual inspection.
Finally, Charger included code that would check if the app ran inside Android emulators, and stop the ransomware from triggering. That is most probably the characteristic that allowed Charger to bypass Bouncer, the Play Store’s security scanner.
Charger averted a number of former Soviet states
All the above are superior options, normally present in desktop ransomware. Moreover, similar to lots of desktop ransomware, Charger included checks that prevented the ransomware from executing if the phone’s owner was from countries such as Russia, Belarus, or Ukraine.
“That is seemingly performed to maintain the builders from being prosecuted in their very own nations or being extradited between nations,” mentioned Oren Koriat and Andrey Polkovnichenko, the two-Test Level researchers that analyzed this menace.


